
Proof of Presence
Log Proof of Presence in Real Time
The EIDOS Proof of Presence app is an effective and efficient solution for generating attendance records for members of staff such as cleaners & security contractors.
Flexible Route Implementation
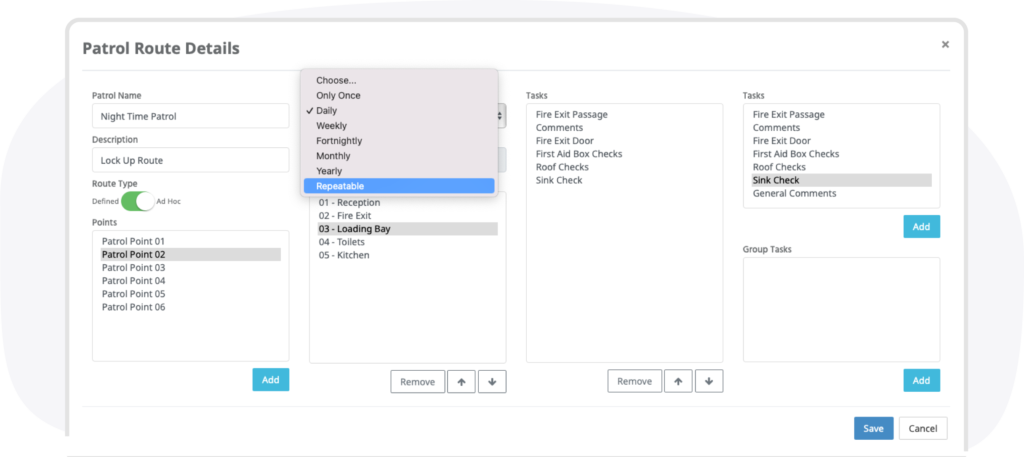
The EIDOS Proof of Presence module is very flexible in the way routes can be configured. They can be ad-hoc giving the user the ability to scan points in their chosen order. Alternatively routes can be defined so that they are completed in a pre-determined sequence.
Routes can be scheduled to be performed on specific days & times or can simply be set to ‘Repeatable’ allowing the user to complete a patrol as many times as they wish. In addition to this it is also possible for a user to create their own ad-hoc patrol from the app.
Simple to Use
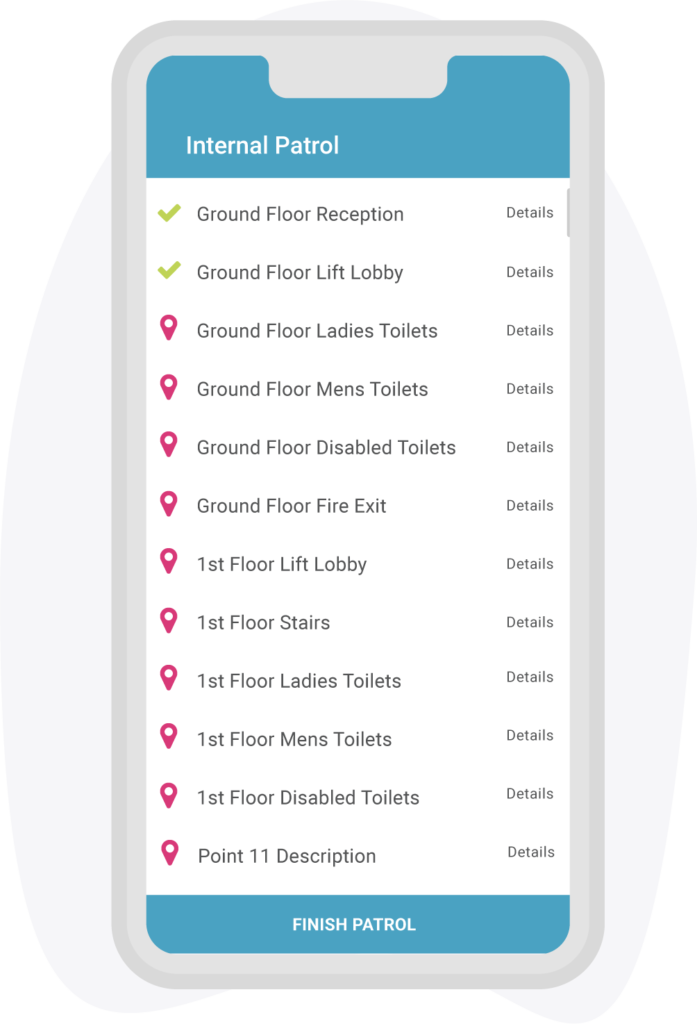
Using the EIDOS app installed on a smartphone the user simply swipes the NFC checkpoints located around the premises. The information is then automatically uploaded to the cloud in real time and can be viewed on a web browser.
Compliance Tasks
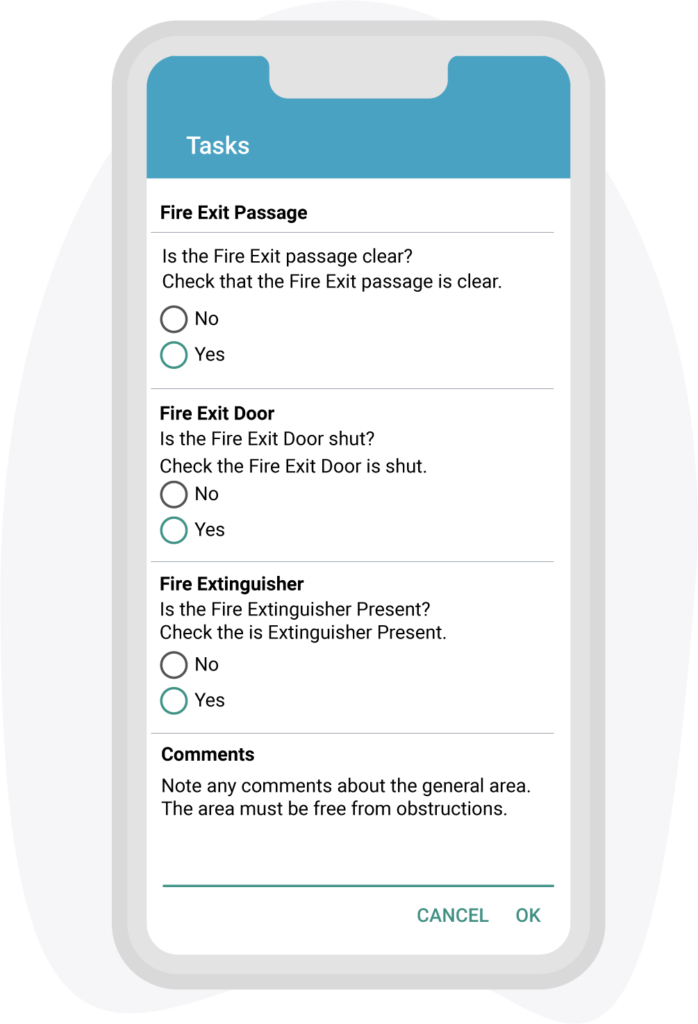
It is also possible to demonstrate compliance by allocating tasks & questions to specific points on a patrol. Where regular checks are required for items such as fire extinguishers, patrol routes can be created from assets held in the optional EIDOS asset management module.
Access the eDOB
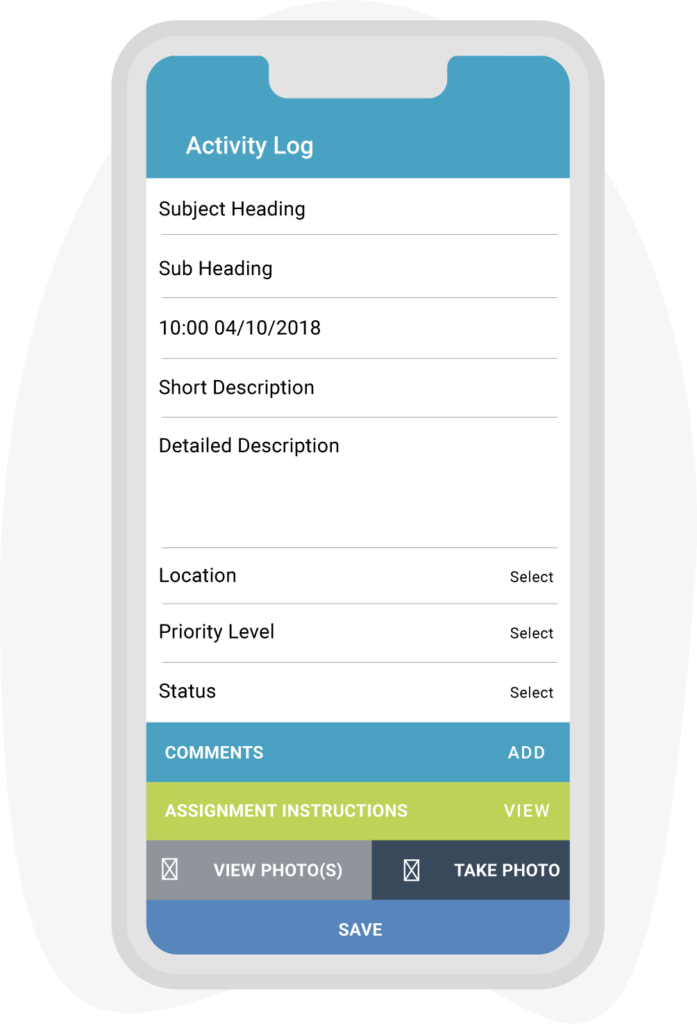
Receive notifications and log faults & incidents plus upload supporting images directly to the Activity Log.
Arrange a Demo
Contact us to arrange a demo either face to face or via your preferred online communications platform.

Search & Manage Data
Efficient Data Management Through Search and Export Features

Export
In depth export to MS Excel.

Review
Review data using the built in dashboard or run live reports via MS Power Bi.

Search
Search and organise data by Subject Heading, Comments, Date & Time, Operator, Location, Priority or Status.

Mobile Data & WiFi
Over 10 Years of Extensive Development
Over the last 10 years we have invested a considerable amount of time and energy in the development and testing of our mobile applications to ensure they’re as stable and reliable as possible. Data dropouts in areas such as basements where no WiFi or mobile signals are available are dealt with by buffering the data until a connection is re-established.
A data SIM isn’t necessary and if you’re not concerned about receiving live data you only need a WiFi signal at the start and end of a patrol.
NFC Patrol Points
Internal
For internal application we suggest the slim 28mm diameter hard PVC tag supplied in either white or black. Supplied with an adhesive backing but can also be attached using the fixing hole in the centre.
External
For external application we suggest the heavy duty 34mm diameter hard PVC tag supplied in black. Will work on metal surfaces and is supplied with an adhesive backing but can also be attached using the fixing hole in the centre.

Near Field Communication (NFC) Explained
NFC (Near Field Communication) is a technology that allows for wireless communication between devices that are in close proximity to each other. In the context of proof of presence, NFC can be used to verify that a person is physically present at a certain location. This can be done by having the person tap their NFC-enabled device (such as a smartphone) on an NFC reader that is located at the location in question. The reader can then confirm that the device’s NFC chip is within range, thereby confirming that the person holding the device is present at the location.

Recommended Phones
From past experience we’ve seen that ‘Ruggedised’ Chinese Android phones are not all they’re cracked up to be (if you pardon the pun). Some of the main concerns include:
- Privacy and security: Some experts have raised concerns about the potential for Chinese-made Android phones to collect and transmit personal data to the Chinese government. There have also been reports of pre-installed malware on some Chinese-made phones, which can compromise users’ privacy and security.
- Quality control: Chinese-made Android phones have sometimes been criticised for not having the same level of quality control as phones made by more established brands. This can lead to issues such as malfunctioning components or poor build quality.
- Lack of software updates: Some Chinese-made Android phones may not receive timely software updates, which can leave them vulnerable to security vulnerabilities and can also affect the user experience.
- Intellectual property infringement: There have been cases where some Chinese-made Android phones have been found to be infringing on the intellectual property of other companies, such as copying the design of iPhone.
- Lack of standard safety certifications: Some Chinese-made Android phones may not have the standard safety certifications that phones made by more established brands have, which can be a concern for users who are concerned about the safety of the product.
It’s important to note that not all Chinese-made Android phones have these issues and some Chinese companies have been praised for the quality of their products, but it’s always good to be informed and aware of the potential risks before making a purchase.
We only supply recognised & established brands. Currently we supply the Samsung Galaxy A04s with a shockproof protective case. If you wish to source your own phone we would always recommend the tried and tested Samsung Galaxy range. Just make sure it has NFC capability.
Download the App
Our apps are only available for Android devices on the Google Play Store. For security reasons you will require an APK key to unlock the app the first time you use it. This can be obtained by contacting support@verifi-eidos.co.uk
Setup, Installation & Training
We want to get you up and running as soon as possible which is why when you place an order with us we’ll ask you for a list of patrol points descriptions. Once we’ve received your list we’ll pre-programme the NFC points and send them ahead of our site visit for you to install. With the points installed we’re able to concentrate on setup and training ensuring you get the most from the system.

Licensing
The annual licence is for a site rather than the number of users which is unlimited.

Developed & Hosted in the UK
Developed & hosted in the UK and is fully GDPR compliant.

Ongoing Support
Being cloud based, updates and enhancements are included as part of the annual license subscription, along with telephone support throughout the year.

Software
Because the software is cloud based there is no need to install software on a PC. You just need a PC with a web browser and internet connection.


